What is LAMP?
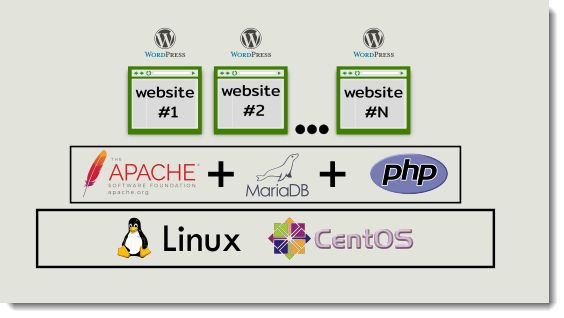
For those of you who don’t know, LAMP stands for Linux, Apache, MySQL and PHP, a lovely combination of tools which allows you to start your learning adventure having multiple paths to follow, you can decide to just learn about Relational Databases and how to create the most functional queries, or you can decide to just play around with the creation of websites, or, why not to go a little bit further merging both worlds to develop web applications putting your hands on both the back end and also the front end, yes! You can become a full stack developer using LAMP.
On top of LAMP we’re going to install WordPress, and we are going to cover the building of a brand new website step-by-step.